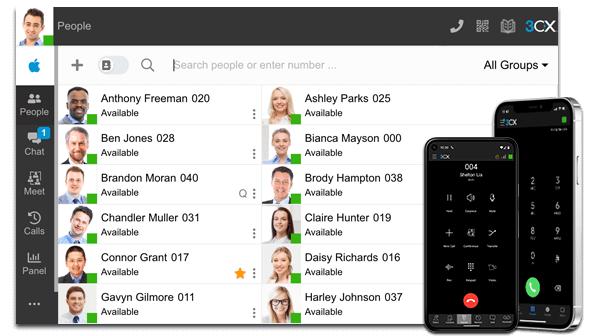
On Wednesday evening, March 29, 2023, we were notified of a serious leak in the Desktop application of one of our VOIP solutions, 3CX.
In versions 18.12.407 and 18.12.416 for Windows and 18.11.1213 for macOS, malicious parties have placed malware to gain further access to systems. In the meantime, we recommend using fixed devices, the mobile app and/or the web application. How the malware could be added has not been disclosed. 3CX said it is conducting an investigation and will provide more information at a later date.
From Analyst ICT we immediately checked all telephone exchanges and we found that none of our end-users are using the infected version of the 3CX Desktop Client. This means that we can cautiously conclude that no damage or break-in has taken place via the 3CX Desktop Client.
We continuously monitor the latest news and will act immediately if action is required. If you still have questions and/or comments about the above news, please contact us by phone or e-mail contact up. Below is the press release from www.security.nl
Security firms sound alarm over malware in desktop application 3CX - update
A library used by 3CX for its Windows application has been infected with malware, the company reveals in a warning know. That is now working on a new Windows app. In the meantime, customers are advised to use the Web application. How the malware could have been added has not been disclosed. 3CX says it is investigating and will come up with more information later today.
The malware added to the desktop application downloads additional malware that steals information from the infected system and can give attackers further access, security companies warn SentinelOne, Sophos and Crowdstrike. The latter party suspects that the attack is the work of a state actor.
Update
The installer of the macOS version of the desktop application was also provided with malware by the attackers, so report security researcher Patrick Wardle and 3CX ceo Nick Galea.